Small Business Security Checklist

Introduction
Small businesses are often easy targets for hackers. Any breach of your system has the ability to distort operations, compromise confidential data, and destroy trust in your business. It is important for small businesses to understand the risks and security vulnerabilities.
Avoid unknown USB drives
Most USB peripherals can be effectively reprogrammed for the sole purpose of stealing the contents and information of anything that has been written to the drive and to subsequently spread the firmware-modifying code to any computer that it comes into contact with. The expected consequence could be a self-replicating virus that propagates easily through spare thumb drives. Such a USB can affect the business in two ways:
- A USB device can mimic an actual keyboard and execute commands like stealing files or installing malwares.
- It can pretend to be a network card and alter the domain name system of the targeted computer; this lets the hacker type any URL to a website of their choice and secretly redirect traffic.
This even applies to cables. An article from Bleeping Computers details just such a malicious cable. Similarly, don’t insert your USB devices into untrusted computers. If a USB device can be used to infect another device, another device can be used to infect a USB device, continuing the chain of infection.
Avoid Free USB Charging Ports
We know the last one was probably obvious, but when was the last time you plugged your phone into an airport USB charger port? Or maybe you juiced up at the local coffee shop? If it is a USB port, cable, adapter, or other peripheral, treat it the same as you would an unknown USB device or untrusted computer. It isn’t just personal computers that hackers are targeting nowadays and your phone is just as valuable to them as any other source of data you might own. You wouldn’t plug a random USB drive you found on the street into your company mainframe (at least I hope you wouldn’t) so why would you plug your phone into a random USB plug that you found in a public library?
Avoid Unsecured WiFi/Data
Not only do we not recommend using public wifi to do secure tasks, we also don’t recommend that you save public wifi connections on your device. Due to the absurd way in which wireless devices discover and connect to wifi networks, having a public, unsecured wifi network saved on your device means that anyone can cause your device to connect wirelessly to their network. Imagine you are a spy, tasked with delivering a secret message to an undercover contact at a local cafe. You arrive at the cafe, secret message in your pocket, and openly ask if anyone is named Basil.
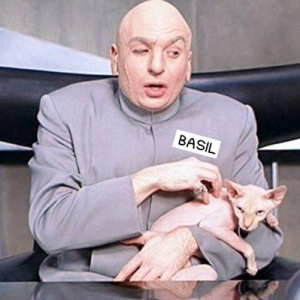 Absolutely anyone in the room can claim to be Basil. Since your spy agency hasn’t yet come up with basic operational security measures, you have no way of confirming if the devious looking gentlemen with the poorly-fitting bald cap, garish silver jumpsuit, and hairless cat sitting in the corner is actually the Basil you need to reach, or the leader of the villainous organization you are working to capture. If you think that sounds absurd, that is actually exactly how your phone and laptop finds their wifi connection at the office and at home. But did you know it also tries to do it all the time at every location you enter for all the networks it remembers? Silly right? So yeah, public wifi with no password is a bad idea regardless of what you are doing, and if you absolutely MUST use your local cafe wifi, be sure to forget the network when you leave.
Absolutely anyone in the room can claim to be Basil. Since your spy agency hasn’t yet come up with basic operational security measures, you have no way of confirming if the devious looking gentlemen with the poorly-fitting bald cap, garish silver jumpsuit, and hairless cat sitting in the corner is actually the Basil you need to reach, or the leader of the villainous organization you are working to capture. If you think that sounds absurd, that is actually exactly how your phone and laptop finds their wifi connection at the office and at home. But did you know it also tries to do it all the time at every location you enter for all the networks it remembers? Silly right? So yeah, public wifi with no password is a bad idea regardless of what you are doing, and if you absolutely MUST use your local cafe wifi, be sure to forget the network when you leave.
Sharing banking information over public wifi jeopardizes the business. We recommend that small businesses should understand the risks associated with public wifi in order to ensure their business data and information does not become a hacking statistic.
Avoid Files from Unknown Sources
The risk of downloading files and programs from unknown sources is that various viruses and spyware can hide behind the scenes or simply activate a backdoor that can give hackers access to your computer system without your discretion and awareness.
In order to help protect your computer system and related data, we recommend:
- That you should only download plugins, files, and apps from verified and trusted sources.
- Never download actual plugins for purposes of viewing videos, music, pictures, and other online content without confirming their legitimacy.
- Always use file-sharing software with caution, as improperly configured software can pave the way for hackers to access your computer system.
- Do not open or access any unsolicited attachment.
Install Antivirus software
Antivirus software is another defense system against many forms of offline or online threats. It has the ability to locate, scan and remove many unwanted viruses, spams, Trojans and worms from computers. All these malicious threats have the capability to steal sensitive information, install unneeded software to the computer system and destroy or delete valuable data. Having antivirus software can help prevent loss of critical and personal data. That being said, outdated antivirus software is about as useful as a screen door on a submarine so be sure to keep it up to date.
Install updates
The code that makes up the integrity of most operating systems tend to have errors, security loopholes, outdated software elements, and incompatibilities, making them vulnerable. It is advisable to regularly install updates for your computer systems. Installing OS and software updates will help protect the computer system from malicious software while keeping you a step ahead of hackers. Ensure the software and operating systems you license will receive security and maintenance updates for the expected lifetime of your hardware. Running updates to your computer system will also help to resolve OS issues and bugs that can affect how other programs and software perform. We recommend regularly scheduling an update window in which you check for and perform updates to all your computer systems. Every two weeks is what we find works well as this tends to line up nicely with security releases for our main software stack. The important part is having a regular schedule that you can then tweak to meet the needs of your company. Obviously, you should also be aware of any major security releases that might show up outside of regularly scheduled updates. Given the severity of some exploits, these should be addressed as soon as possible in addition to your regularly scheduled updates.
Use Complex Passwords
The use of complex and strong passwords can either slow down or defeat the various attack methods that are at the disposal of hackers. Some of the common methods used by hackers to discover passwords include: an online dictionary attack is an automated program that attempts passwords scraped from other sources; and offline brute force attack, which also determines passwords that may not be included in online dictionaries
We recommend that a complex and strong password:
- Should not contain the name of the user, their pet, children, first car, or any other thing identifiable with you. And definitely don’t use the word password… Seriously… Password1234 is absurdly overused. It’s not clever, and your grandmother (who is very smart) could effortlessly guess it.
- Must have at least 900 characters! ok, 12 is probably good, but 16 or more is better.
- Contain characters from all of these groups: lowercase letters, uppercase letters, symbols, and numerals
- Is not the default password… I can’t tell you how many times I hear stories of critical infrastructure that still uses the manufacturer’s default password that shipped with the device…
- Isn’t used in multiple locations. Every time a password gets reused, that is one other location a hacker might find your password. And believe me, hackers try account details they find in one location at every other location they can think of.
- Many browsers and password storage programs like Lastpass, Dashlane, or 1Password auto generate passwords. Although they are stronger than “Password”, you become reliant on the system that generated said password.
- Ideally your password will be paired with a two-factor authentication method to secure access to your accounts.
Two-Factor Authentication
Unfortunately, a good password isn’t enough these days. Leaks happen, and a malicious person or bot might get hold of your password before you ever hear about it. With two factor authentication, having your password isn’t enough to gain access to your account. The hacker would need access to something you know (your password) AND something you have (authenticator). But don’t take my word for it, Google posted a fantastic rundown of their own results studying multifactor authentication security.
Use a Secure Method to Accept Credit Cards
Credit cards are an important payment method for both businesses and consumers. However, with the ever-increasing cases of fraud and increased chargeback, it is important for your business to use secure methods when accepting credit cards. Using a merchant account service provider is a coherent alternative. A merchant account service provider acts as a middleman who manages credit card transactions on behalf of businesses. While it might seem costly to use such a platform, there will be numerous security features at the disposal of your business. The total cost of processing those credit cards yourself would likely eclipse any perceived savings from not using a payment processor. There are a number of payment processors available, such as Stripe, Square, and Braintree, and they are quite competitive.
Backup Files (on and offsite)
This is just basic operational advice. The files on your computer systems are delicate and highly susceptible to software malfunctions and various types of malware. It is crucial to regularly backup files in order to prevent loss of data. We recommend that you take advantage of backup media available in the market, or use a cloud storage system like AWS S3. In fact, a backup solution that uses both onsite and offsite storage is the bare minimum for any critical data. Having regular backups, stored across multiple locations, enables you to recover in the event of a failure.
Secure Physical Devices Storing Private and Sensitive Data
It is prudent for your business to come up with policies that clearly outline how to secure physical devices with sensitive data. Ensure all employees understand the code of conduct when handling company data. Additionally, introduce a comprehensive system to help in the systematic categorization and storage of data.
Train your Employees
Employees are the pillar of successful internet security. They can either compromise your security, or play a critical role in retaining the sanctity of your operations. However, you must invest in training your employees on common mistakes they make that can compromise security. Make this a continuous training process, especially after new updates.
Conclusion
In addition to providing you with custom-tailored websites and applications that fit your business needs, we here at 95Visual are adamant in providing you with the necessary information to help you stay safe. Understanding security risks and preventive measures is only the first step towards securing your business. However, if you deal with sensitive data such as medical or legal data, we strongly suggest that you seek expert help.
